What To Do When A Credit Agency Equifax Up?
~8 min read
If you led a major American company in an industry that believed itself to be largely immune from consequences, waiting one month until news attention was focused on a major hurricane, just before the annual 9/11 commemorations, to announce that you had allowed your customers' most valuable assets to be stolen probably seemed like a good idea. You could probably even get away with proposing to immunize yourself from class action suits and charge your customers for the privilege of being kept safe from the consequences of your mistakes.
Heck, even dumping your shares before the news was made public (though probably unwise because of the potential outward appearance of insider trading) has a certain internal logic. You might even be so bold as to tell investors that the company remained “committed to delivering on the long term financial model of 7-10% revenue growth." But, really, why the confidence?
High Value Products?
Equifax’s long term financial model reflects our continuing fundamental ability to utilize our unique and differentiated data assets and leading analytical capability to deliver high value products and services to our customers.Equifax CEO, Richard Smith
There is no reason to believe that Mr. Smith is being disingenuous in his projection quoted above (indeed, there would be serious fiduciary questions to answer if he were), so his words raise some significant questions about the nature of his and Equifax’s business.
Chief among these concerns is, how can a company whose main line of business is to guard customers’ data, so as to authenticate their identities and assess their credit worthiness, lose that very same data and still be confident of meeting its growth projections? The damage done to Equifax’s market cap, losing approximately 21% since last Thursday, is pretty horrific, but on another level what’s astonishing is that it’s not worse. Whatever the public and media are making of Mr. Smith’s apologies, (“This is clearly a disappointing event for our company… I apologize for the concern and frustration this causes.”), the markets are putting considerable store ($17.5bn) in his ability to deliver on the pre-hack long-term financial model.
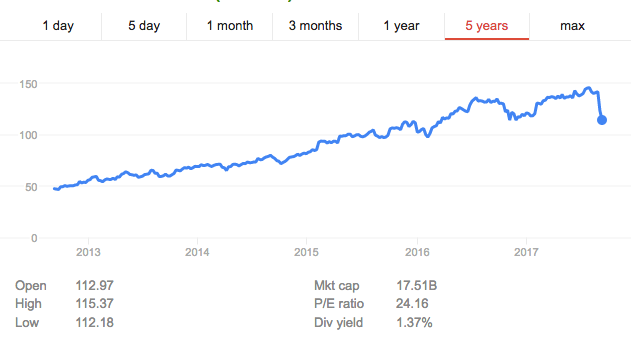
Source: Google
The clue to Equifax’s remarkable bullishness relies on the interplay between three items named by Smith: data assets, analytical capability and customers. For while Equifax undoubtedly has proprietary data analytic capabilities, they are worth little without data to analyze and customers to pay for the analysis.
So, while copies of some of the most valuable identifying information for 143 million Americans (in addition to an undisclosed number of Canadians and Britons) has been leaked and is likely to be soon available for purchase in the seedy corners of the Dark Web, Equifax still remains in possession of the original data, and can continue to “analyze” it in a fashion that generates hundreds of millions of dollars in revenues for the benefit of its customers.
Who Are The Customers?
To a large extent these customers are not the consumers whose data is analyzed, but rather other businesses who want credit reports and other information on same said customers. In short, unless there is a flight away from Equifax in the B2B sector, it is likely to remain business as usual for the company. But what would be the fate of an employee who left 143 names, addresses and social security numbers (SSNs) in the back of a cab?
From pretty much whichever angle you look at it from, this sounds very much like an industry that is screaming out not just for disruption, but for a revolution. Social security numbers were never meant to be used to get a cell phone or broadband contract, to open a bank account or see a doctor. So it should come as no surprise that using 1930s-technology in the digital age for a purpose for which it was never intended didn’t end well. By way of contrast, consider this list of entities that the British government states need to have sight of the UK’s equivalent of a SSN:
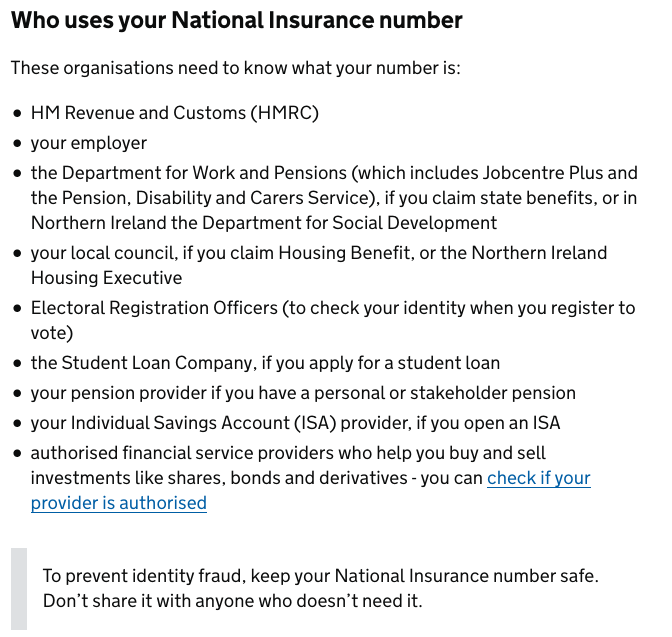
UK Government advice on sharing National Insurance numbers
So can the digital transformation offer salvation from an uncompetitive industry that apparently feels immune from failure on a massive scale?
Digital Solutions?
The uncomfortable answer is probably not anytime soon, unless either consumers wage an almost unprecedented campaign of action to withhold their business from Equifax and companies that use it, or alternatively there is intervention from the federal government. At the moment neither seems very likely, and even then it is not entirely clear how Equifax’s demise - while its business model continues on via the other two main credit rating agencies (Experian and TransUnion) but with less competition - really solves the matter. Part of the problem is that there is no obvious, viable alternative standing in the wings in the U.S. ready to answer the call to action from an outraged public or interventionist government.
On the fringes of Finovate Fall in New York, Mondato spoke to Ted Ross, CEO of SpyCloud, an intelligence analytics company that alerts businesses when their systems and data have been compromised. Mr. Ross told Mondato Insight that unfortunately the problem was not confined to Equifax or the credit reporting business, and that the problem seems to be getting worse rather than better.
The larger the organization, the more they install, the more they need to maintain, the higher the chances of failure. I get that Equifax is still responsible, but I also don’t believe that they are unique in their vulnerable position.Ted Ross, CEO SpyCloud
So given the systemic nature of the problem, is any jurisdiction providing effective alternatives to SSN-style authentication challenges? Thankfully, yes. The leader of the pack is Estonia, sandwiched between Latvia and Russia, whose government embarked several years ago on a pioneering program of government digitization. The Estonian government’s X-Road IT platform (using the X.509 cryptography standard) allows Estonian residents and citizens to securely access around 4,000 different services, from banking to taxes to managing business and medical records, all using a government-issued ID card containing a microchip, and a USB-ported card reader.

"E-stonia" is a very plugged-in nation
If you are still skeptical, you can try it out for yourself, by becoming an e-resident of Estonia. Just a few minutes online and €100 will start the application process to get you an Estonian e-residency card, even if you have never been there, that allows you to access many of the digital services that are open to citizens, including opening bank accounts and businesses.
But of course, just because this system works in a country with a smaller population than the Bronx, that certainly doesn’t mean the technology is sufficiently sound to work somewhere as big as the United States. With no disrespect intended to Estonia, the cost-benefit calculation for hacking America’s hypothetical ID cards is vastly different from hacking Estonia’s actual ID cards. Just last week, a security flaw was reported in an estimated 750,000 Estonian ID cards, but luckily for Estonia it was a group of academic cryptographers who made the discovery, and not a fabled malevolent Russian hacker.
Knowing the public key of the certificate is not enough to unlock the card – powerful and expensive computing power to calculate the secret key and special custom-made software for signing are also needed… The reported vulnerability is significant due to the increase in computing power in recent years. A few years ago, exploiting such a vulnerability would have been significantly more expensive and thus more unlikely than it was today.The Republic of Estonia Information System Authority
Nevertheless, an extra layer of authentication, from something as basic as a PIN or password, to a mobile push notification or even biometrics such as Touch ID fingerprint, facial or voice-recognition software, all take the security of the system far beyond anything currently available in the United States, where the proffering of “the last four of your Social” can be as sophisticated, and therefore vulnerable, as authentication gets. (Though the limits of biometrics were cruelly put on display by a live demo fail at the launch of the latest iPhone.)
Definitely Not E-Merica
And as nice as the idea is, you don’t have to be a libertarian to see that a national ID system is never going to fly in the United States, which to some optimists and entrepreneurs means that perhaps micro-chipped ID-cards themselves are a legacy form of late-20th century tech masquerading as a 21st century solution. Could, instead, the blockchain hold the answer?
At a conceptual level, the blockchain and “self-sovereign identity” appear to go together like fireworks and the 4th of July, with the result that there are some blockchain ID evangelists out there, but in reality they are relatively thin on the ground. The reason is simple: a blockchain-based ID will face the same obstacles that an X.509-based card does.
A trusted entity will need to establish some legal and enforceable rules and policies for how it all works, they’ll need to make it easy for the average person to use securely, and they’ll need to convince a critical mass of people and service providers to adopt and trust the ID — all while finding an economically viable business model.Charles Race, President Worldwide Field Operations, Okta
Hope on the Horizon?
So how serious is the problem, Equifax aside? Mr. Ross's colleague, Jason Lancaster, Director of Security Research at SpyCloud, told Mondato Insight,
"These breaches happen every day - just a look at the SpyCloud breach catalog containing 9 billion records. This shows clearly that there’s already massive amounts of PII and valid credentials available in the Underground. This is reflective of the current state of cyber security. This is likely not to improve any time soon.Jason Lancaster, Director of Security Research, SpyCloud
So, depressingly, if you live in the US (and maybe if you live in the UK or Canada), you should assume from here on out that hackers have your name, address, mobile number, SSN and driving license number, and that they will probably try and exploit that data for their own criminal enrichment. But aside from getting sick at the thought, is there anything you can actually do about it?
For the time being, the best advice seems to be to put a freeze on your info at all known credit agencies, although this will cost money; somewhat brazenly, Equifax will charge you $30 for the privilege. Nevertheless, this means that no new credit check can be passed in your name without you removing the freeze. The default response will be “Computer Says No”, which is probably as it should be. Additionally, there are services available to consumers and businesses from companies such as SpyCloud, that will give early warnings about compromised information, allowing the parties concerned to make informed decisions about harm mitigation.
The only hope then, in the short- to medium-term is governmental action, which is unlikely in the current political maelstrom. But who knows? Stranger things have happened: Equifax lost everyone's personal info and didn't let anyone know for a month. That remains pretty unbelievable on so many levels.
Click here to subscribe and receive a weekly Mondato Insight direct to your inbox.

Finovate Fall: Fintech = Financial Inclusion?
When Telcos and FSPs Intersect